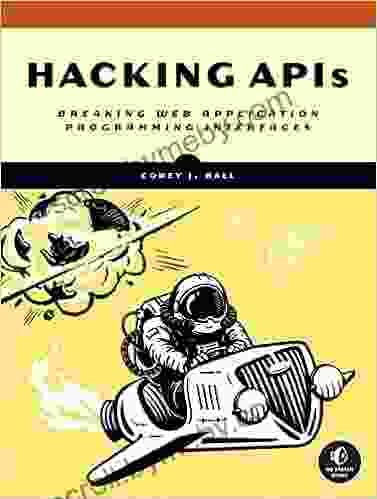
Hacking APIs: Breaking Web Application Programming Interfaces

Web application programming interfaces (APIs) have become essential components of modern web development. They provide a means for different applications and services to communicate with each other, enabling seamless integration and data sharing. However, APIs also introduce a potential security risk, as they can be exploited by attackers to gain unauthorized access to sensitive data or disrupt the functionality of an application.
5 out of 5
| Language | : | English |
| Text-to-Speech | : | Enabled |
In this comprehensive guide, we will delve into the techniques used by hackers to exploit vulnerabilities in APIs. We will explore various hacking methodologies, analyze real-world examples, and provide practical guidance on how to secure your APIs against these attacks.
Chapter 1: to API Hacking
In this chapter, we will provide an overview of API hacking, including its motivations, common attack vectors, and the potential impact of API breaches. We will also discuss the different types of APIs and their inherent security risks.
Chapter 2: Reconnaissance and Vulnerability Assessment
Before launching an attack, hackers typically conduct reconnaissance and vulnerability assessment to identify potential targets and gather information about their APIs. In this chapter, we will cover the techniques used for API reconnaissance, including web scraping, API documentation analysis, and fuzzing.
Chapter 3: Common API Hacking Techniques
In this chapter, we will explore the most common API hacking techniques, such as parameter tampering, injection attacks, authentication bypass, and denial-of-service attacks. We will provide detailed examples of each technique and discuss how to mitigate them.
Chapter 4: Real-World API Hacking Case Studies
In this chapter, we will analyze real-world API hacking case studies to illustrate the practical application of the techniques discussed in the previous chapters. We will examine how hackers exploited vulnerabilities in popular APIs and the consequences of these attacks.
Chapter 5: API Security Best Practices
In this chapter, we will provide practical guidance on how to secure your APIs against hacking attacks. We will cover best practices for API design, implementation, and ongoing maintenance. We will also discuss the importance of API security testing and monitoring.
By understanding the techniques used by hackers and implementing robust security measures, you can protect your APIs from unauthorized access and ensure the integrity of your applications and data.
This guide is an essential resource for anyone involved in web application development, security, or risk management. By following the advice provided in this book, you can significantly reduce the risk of API breaches and protect your organization from the damaging consequences of data theft, financial loss, and reputational damage.
Free Download Your Copy Today!
Click here to Free Download your copy of Hacking APIs: Breaking Web Application Programming Interfaces today.
5 out of 5
| Language | : | English |
| Text-to-Speech | : | Enabled |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Courtney Friel
Courtney Friel Clifford D Simak
Clifford D Simak Dale Hudson
Dale Hudson T L Payne
T L Payne Craig Hatkoff
Craig Hatkoff J C Sum
J C Sum Paul Haddad
Paul Haddad Cynthia Royce
Cynthia Royce Cyndi Kinney
Cyndi Kinney Rusty Ferguson
Rusty Ferguson Joshua W Cotter
Joshua W Cotter Lisa Morgan
Lisa Morgan Gabriele Carboni
Gabriele Carboni Department Of The Army
Department Of The Army Stephen Book
Stephen Book Corey Yoder
Corey Yoder Dale Pollock
Dale Pollock Creative Guy
Creative Guy Nel Noddings
Nel Noddings Robert L Mcdonald
Robert L Mcdonald
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Rudyard KiplingJourney Into the Enchanted Realm: Unlocking the Magic of "How to Train Your...
Rudyard KiplingJourney Into the Enchanted Realm: Unlocking the Magic of "How to Train Your...
 Robert Louis StevensonUnleash the Magic: Discover the Art of Pack Flat Illusions for Captivating...
Robert Louis StevensonUnleash the Magic: Discover the Art of Pack Flat Illusions for Captivating...
 James HayesUnveiling the Extraordinary Journey of Naomi Osaka: An In-Depth Exploration...
James HayesUnveiling the Extraordinary Journey of Naomi Osaka: An In-Depth Exploration... John SteinbeckFollow ·15.7k
John SteinbeckFollow ·15.7k Gabriel BlairFollow ·18k
Gabriel BlairFollow ·18k Branson CarterFollow ·19.9k
Branson CarterFollow ·19.9k Angelo WardFollow ·19.4k
Angelo WardFollow ·19.4k Duane KellyFollow ·6.2k
Duane KellyFollow ·6.2k Eric NelsonFollow ·5.2k
Eric NelsonFollow ·5.2k Isaiah PriceFollow ·19.2k
Isaiah PriceFollow ·19.2k Julian PowellFollow ·8.2k
Julian PowellFollow ·8.2k
 Cruz Simmons
Cruz SimmonsUnveiling the Secrets: An Insider Guide to School Bonds...
Unlock the Power of School...

 Gil Turner
Gil TurnerRuins of Empire: Blood on the Stars - The Epic Space...
Ruins of Empire: Blood on the Stars is the...
 Allen Ginsberg
Allen GinsbergPrepare for the Ultimate Space Opera: Delve into The Last...
Embark on an...
 Anton Foster
Anton FosterUnleash Your Inner Artist: The Ultimate Guide to Oil...
Chapter 1: The...
5 out of 5
| Language | : | English |
| Text-to-Speech | : | Enabled |